Fishing for hackers: Analysis of Linux Server Attack
By A Mystery Man Writer
Description

10 top anti-phishing tools and services

Guide: 📋 How to Hack API in 60 minutes or API Threats Simulation

Haggling With Hackers: Surprising Lessons From 50 Negotiations

Ethical Hacking using Kali Linux

Analysis of Attacks That Install Scanners on Linux SSH Servers
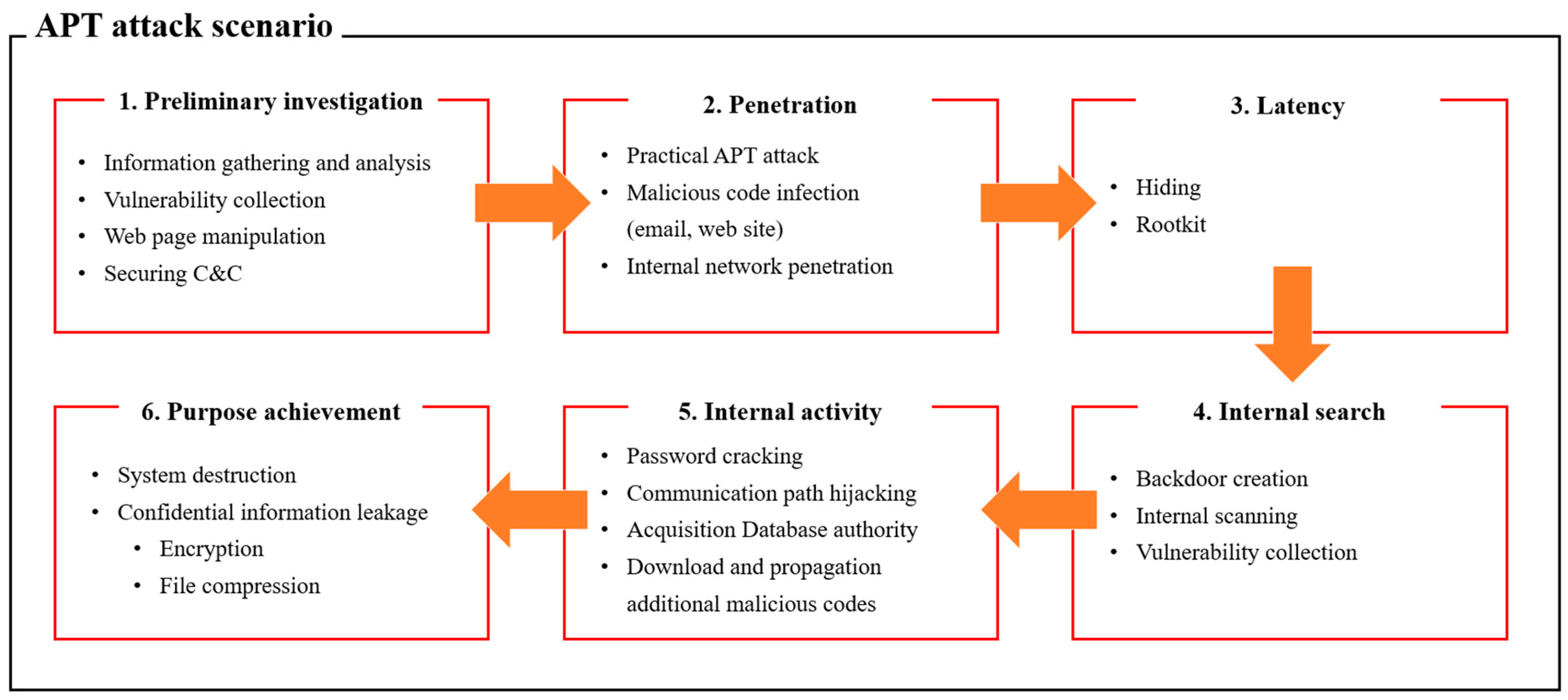
Applied Sciences, Free Full-Text
Ethical Hacking Basics, Ethical Hacking Blogs & Articles

What Is Sandboxing? Working, and Best Practices for 2022 - Spiceworks
phishing-attacks · GitHub Topics · GitHub

hacking: Most laptops vulnerable to attacks via plug-in devices: Study

Analysis of Attacks That Install Scanners on Linux SSH Servers

HHS - Lesson 7 - Attack Analysis - Hacker Highschool

25 Best Kali Linux Tools

The advanced email spoofing attacks of hackers-for-hire group Dark

8 Common Types of Cyber Attack Vectors and How to Avoid Them
from
per adult (price varies by group size)