Popular Phishing Techniques used by Hackers
By A Mystery Man Writer
Description
Common Types of Social Engineering, Phishing Attacks in Healthcare

Top 50 most impersonated brands in phishing attacks and new tools you can use to protect your employees from them

Unit 5 - Cyber Security, PDF, Computer Virus

Cyber Security - CS-503 (C) - Class Notes - 1563265709, PDF, Cybercrime

Cyber Security - CS-503 (C) - Class Notes - 1563265709, PDF, Cybercrime

Whaling vs. Spear Phishing: Key Differences and Similarities - Spiceworks

5 Types of Phishing Attacks and How To Avoid Them - N26
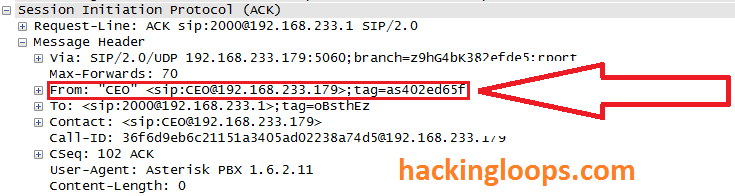
Penetration testing of VoIP : How Hackers Spoof Caller ID

Unit 5 - Cyber Security, PDF, Computer Virus
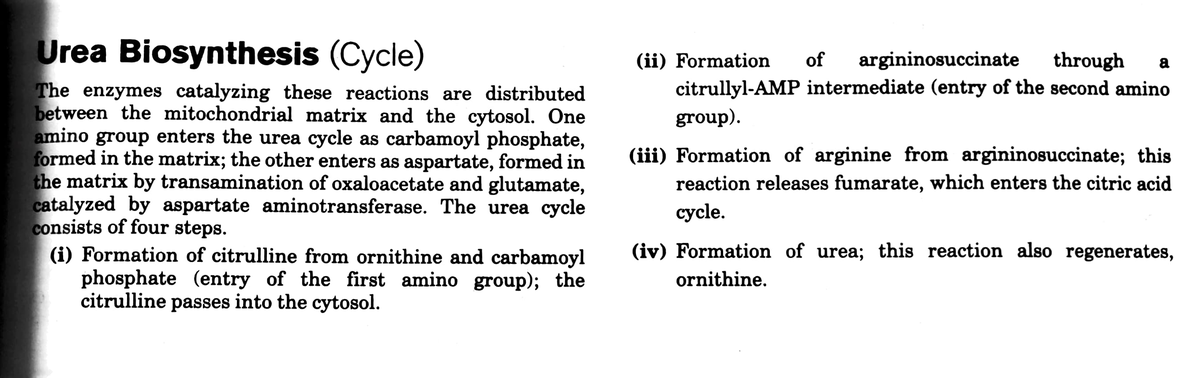
Urea biosynthesis - Urea - Urea Biosynthesis (Cycle) (ii) Formation through a of argininosuccinate - Studocu
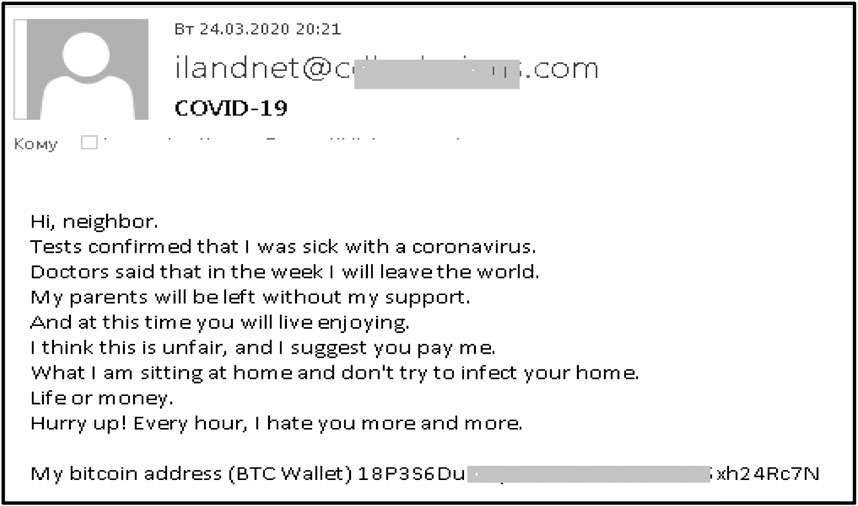
Frontiers Phishing Attacks: A Recent Comprehensive Study and a New Anatomy

Unit 5 - Cyber Security, PDF, Computer Virus
Can Phishing Education Enable Users To Recognize Phishing Attacks, PDF, Phishing

Evolution of Phishing Attacks
from
per adult (price varies by group size)